DEF CON Infosec super-band the Cult of the Dead Cow has released Veilid (pronounced vay-lid), an open source project applications can use to connect up clients and transfer information in a peer-to-peer decentralized manner.
The idea being here that apps – mobile, desktop, web, and headless – can find and talk to each other across the internet privately and securely without having to go through centralized and often corporate-owned systems. Veilid provides code for app developers to drop into their software so that their clients can join and communicate in a peer-to-peer community.
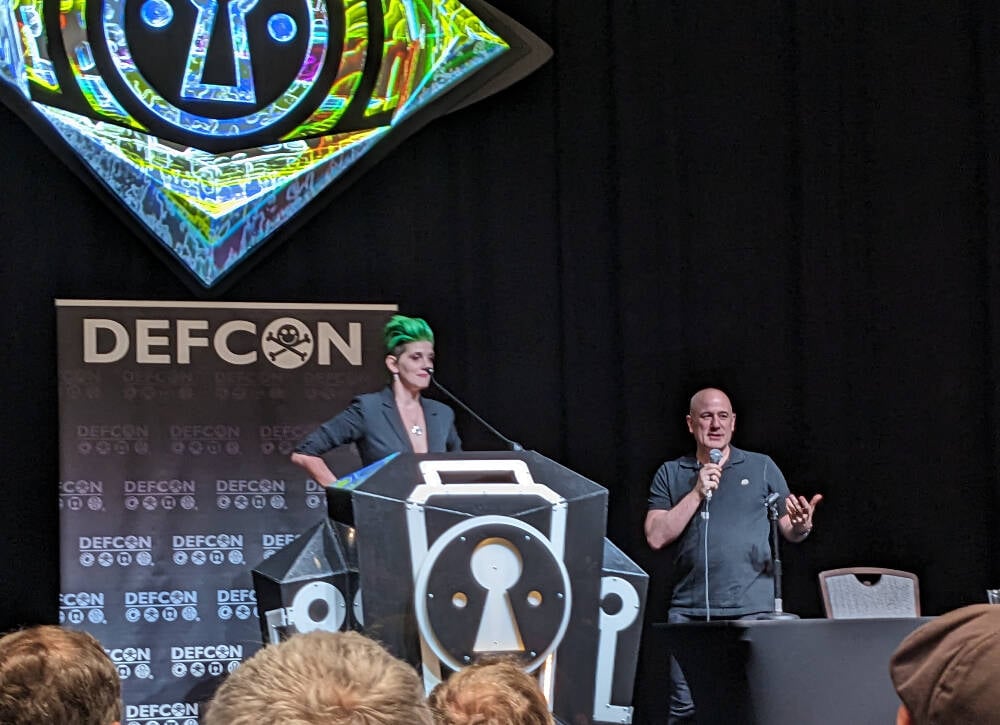
In a DEF CON presentation today, Katelyn “medus4” Bowden and Christien “DilDog” Rioux ran through the technical details of the project, which has apparently taken three years to develop.
The system, written primarily in Rust with some Dart and Python, takes aspects of the Tor anonymizing service and the peer-to-peer InterPlanetary File System (IPFS). If an app on one device connects to an app on another via Veilid, it shouldn’t be possible for either client to know the other’s IP address or location from that connectivity, which is good for privacy, for instance. The app makers can’t get that info, either.
Veilid’s design is documented here, and its source code is here, available under the Mozilla Public License Version 2.0.
“IPFS was not designed with privacy in mind,” Rioux told the DEF CON crowd. “Tor was, but it wasn’t built with performance in mind. And when the NSA runs 100 [Tor] exit nodes, it can fail.”
Unlike Tor, Veilid doesn’t run exit nodes. Each node in the Veilid network is equal, and if the NSA wanted to snoop on Veilid users like it does on Tor users, the Feds would have to monitor the entire network, which hopefully won’t be feasible, even for the No Such Agency. Rioux described it as “like Tor and IPFS had sex and produced this thing.”
“The possibilities here are endless,” added Bowden. “All apps are equal, we’re only as strong as the weakest node and every node is equal. We hope everyone will build on it.”
Each copy of an app using the core Veilid library acts as a network node, it can communicate with other nodes, and uses a 256-bit public key as an ID number. There are no special nodes, and there’s no single point of failure. The project supports Linux, macOS, Windows, Android, iOS, and web apps.
Veilid can talk over UDP and TCP, and connections are authenticated, timestamped, strongly end-to-end encrypted, and digitally signed to prevent eavesdropping, tampering, and impersonation. The cryptography involved has been dubbed VLD0, and uses established algorithms since the project didn’t want to risk introducing weaknesses from “rolling its own,” Rioux said.
This means XChaCha20-Poly1305 for encryption, Elliptic curve25519 for public-private-key authentication and signing, x25519 for DH key exchange, BLAKE3 for cryptographic hashing, and Argon2 for password hash generation. These could be switched out for stronger mechanisms if necessary in future.
Files written to local storage by Veilid are fully encrypted, and encrypted table store APIs are available for developers. Keys for encrypting device data can be password protected.
“The system means there’s no IP address, no tracking, no data collection, and no tracking – that’s the biggest way that people are monetizing your internet use,” Bowden said.
“Billionaires are trying to monetize those connections, and a lot of people are falling for that. We have to make sure this is available,” Bowden continued. The hope is that applications will include Veilid and use it to communicate, so that users can benefit from the network without knowing all the above technical stuff: it should just work for them.
To demonstrate the capabilities of the system, the team built a Veilid-based secure instant-messaging app along the lines of Signal called VeilidChat, using the Flutter framework. Many more apps are needed.
If it takes off in a big way, Veilid could put a big hole in the surveillance capitalism economy. It’s been tried before with mixed or poor results, though the Cult has a reputation for getting stuff done right. ®


The reason is that the “protect the children” thing is and always has been a bad faith excuse to expand or establish control over others. That’s not to say that places like TOR don’t have a problem with CSAM but if that were the actual target, it would be addressed in the proposed laws and vigorously pursued. It never is.
Protecting children is always, at most, a token gesture in these laws, which exand censorship and surveillance of the population, while demonstrating complete disregard for harms and unnecessary risks that they introduce, while generally also exempting those in power from being impacted.
deleted by creator
Indeed.
For a good example of how “extra policing and security” can go too far, go no further than the TSA and all the “terrorism” they protect us from
If that’s what you have to tell yourself, fine. But at least be intellectually honest here and admit you’re simply willing to condone child abuse because you think Google or whatever looking at your texts is more egregious
Nah. I don’t condone it nor do I think its perpetrators should be able to escape justice, regardless of how wealthy or politically connected they are. They deserve the same as slavers for the lifelong harms that they cause their victims. If you’re intellectually honest, you’ll admit that giving unfettered access to personal information and habits to organizations with poor track records of keeping such access safe is a stupid idea.
ETA: While I don’t like that megacorps have my information, that ship has sailed. What I see as the bigger problem is when the backdoor access and data is stolen by criminal organizations or abused by state actors. Think the increasing rate of identity theft, credit card fraud, and ransomware attacks is bad now? You ain’t seen nothing yet. Just wait until a bad actor has access to everyone’s devices and activity data then starts selling it to whoever is interested (burglers knowing when victims will be absent, state actors not needing to even employ a honeypot for blackmail, properties “mysteriously” being signed over to megacorps, groups committing genocide and censoring and mention on electronic media, etc.). Might sound like an exaggerated enumeration of risks but it’s quite the opposite. If you have any understanding of how online services work, you know that encryption and security are the only reason that the Internet can be used for anything beyond sharing documents.
ETA2: Also, if you’ve paid even the slightest bit of attention to history, you’ll know how much “think of the children” was abused in the 20th century alone to try to prevent access to “black music” (jazz, blues), education, art, rock music, knowledge of sex, fantasy novels, roleplaying games, programs preventing child abuse, etc.
This is empty virtue signalling and false equivalency. Just say it. You think there’s a unknowable volume of real life, actually happening, enablement of the pain, suffering, and death of men, women, and children you’re willing to accept so Google or the government or whatever can’t read your irrelevant and unimportant conversations
https://arstechnica.com/information-technology/2019/05/stolen-nsa-hacking-tools-were-used-in-the-wild-14-months-before-shadow-brokers-leak/
https://en.m.wikipedia.org/wiki/2017_Equifax_data_breach
https://www.bbc.com/news/uk-northern-ireland-66467164
https://www.trendmicro.com/vinfo/us/security/news/cyber-attacks/wendy-s-credit-card-breach-across-300-stores-caused-by-pos-malware
https://www.trendmicro.com/vinfo/us/security/news/cyber-attacks/hackers-leak-information-of-30-000-fbi-and-dhs-employees
https://www.techdirt.com/2023/05/24/heritage-foundation-says-that-of-course-gop-will-use-kosa-to-censor-lgbtq-content/
An yes. We should absolutely trust large corporations and state actors to keep our information and backdoors safe, and protect our children by checks notes opening the them up to actions shown to increase suicide./s
Come on, mate. Accusing people of supporting child abuse to try to keep them from speaking out about terrible ideas and manipulative excuses that are put forth in bad faith doesn’t look good on you.
Ok,.cool? 70% of those don’t apply to this conversation at all.
Look, it’s clear you’re willing to twist yourself into a pretzel and play whataboutism because you refuse to acknowledge the uncomfortable truth. That’s fine, I get it.
Nearly every aspect of our society relies on the exploitation and suffering of others.
While I’d disagree strongly on relevance, I’m curious about your justification for ignoring the remainder that clearly shows that megacorps and state actors are not trustworthy with such responsibilities.
You think that wanting policies and laws claiming to protect children to actually be intended and used to protect children is an uncomfortable truth?
Erm… What? Not sure how this is relevant. Are you saying that you’re in favor of exploitation or laws written in bad faith to increase the suffering of others? That you think that we should not try to work towards a safer and more equitable world? Really not clear.